Blog
Mid-Year Cybersecurity Audit: What Financial Services Firms Should Assess
A practical guide to what a meaningful mid-year cybersecurity audit looks like for financial services firms and what to do with the findings.
Understanding Software Bill of Materials (SBOM) Requirements
A clear introduction to what a Software Bill of Materials is, why it matters, and what an SBOM strategy should look like for a regulated firm.
Building Resilient Communication Systems for Remote Teams
An advisory look at what truly resilient remote communication systems look like, and the architectural decisions that separate strong setups from fragile ones.
How IT Tools Support Employee Well-being During Mental Health Awareness Month
A practical look at how thoughtful technology decisions support employee mental health, reduce friction in daily work, and shape a healthier workplace.
The Role of IT in Supporting Neurodivergent Employees
Strategic IT design can remove barriers for neurodivergent employees by building flexibility, accessibility, and customization into the technology environment from the ground up.
Implementing Behavioral Biometrics for Enhanced Authentication
Behavioral biometrics offer financial services firms a way to verify user identity continuously based on how people interact with their devices, not just what they know or have.
Sustainable IT Practices for Financial Services
Financial services firms can reduce costs, strengthen compliance, and future-proof operations by building sustainability into their IT infrastructure strategy.
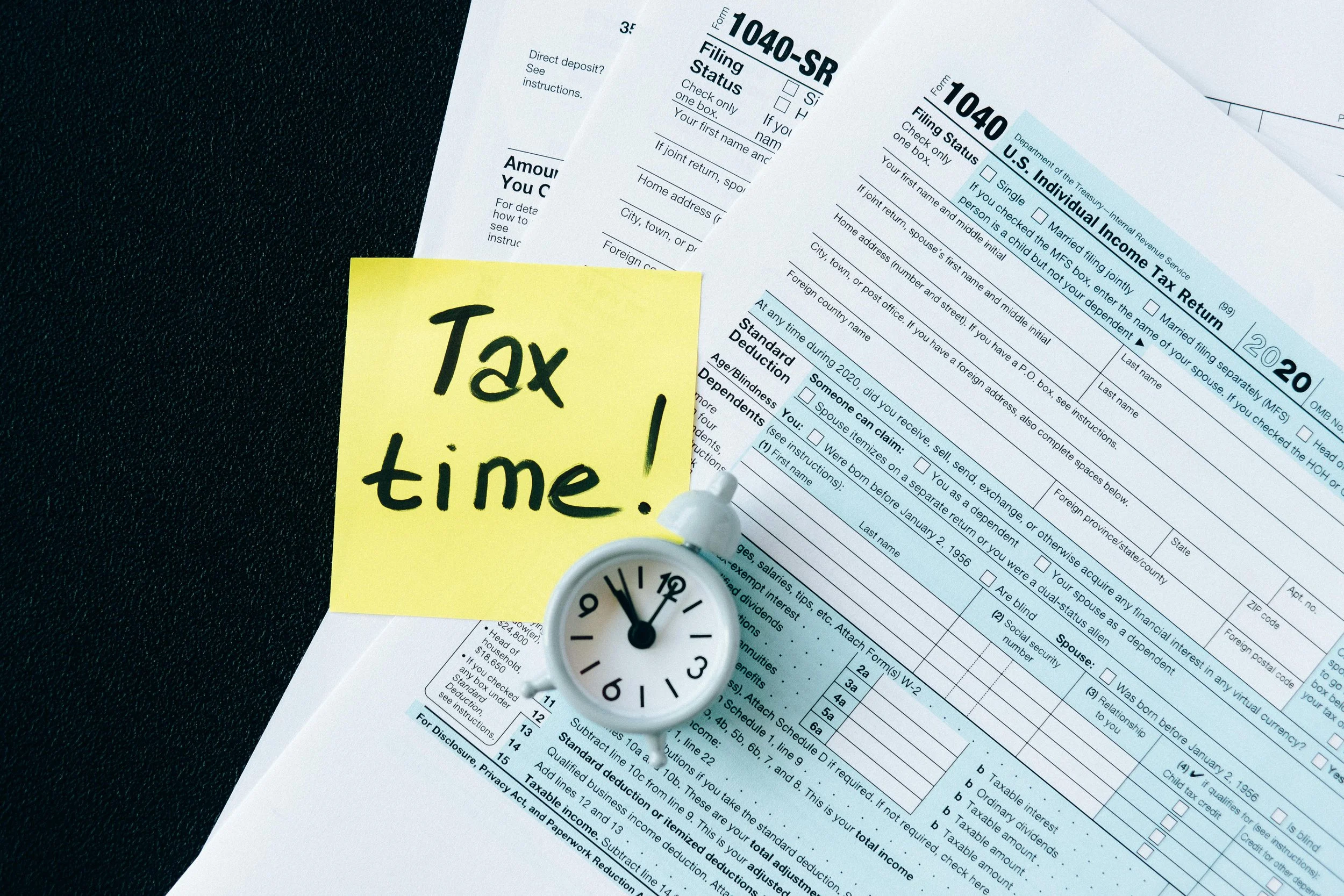
Tax Season Cybersecurity: Protecting Client Data During Peak Times
This blog provides actionable strategies for financial services firms to protect client data during tax season, when cybercriminals aggressively target organizations handling sensitive financial information.
Advanced Persistent Threats: Detection and Response Strategies
This blog examines what advanced persistent threats are, how they differ from common cyberattacks, and the detection and response strategies financial services firms need to defend against them.
Understanding Regulatory Technology (RegTech) for Financial Services
This blog provides a comprehensive overview of regulatory technology (RegTech) for financial services, explaining how these tools streamline compliance, reduce costs, and improve accuracy.
Spring Cleaning Your IT Infrastructure: Maintenance Best Practices
This blog provides a comprehensive guide to spring cleaning your IT infrastructure, covering everything from system audits and patch management to data cleanup and security reviews.
Women in Cybersecurity: Addressing the Talent Gap
This blog examines the cybersecurity talent gap, highlights the critical role women play in strengthening security teams, and offers actionable strategies for organizations looking to build more diverse and effective cybersecurity workforces.
Navigating the Intersection of Privacy and Personalization in Financial Tech
This blog explores how financial services firms can deliver personalized client experiences while maintaining strict data privacy standards and regulatory compliance.
The Growing Importance of Data Residency in Financial Compliance
This blog examines why data residency has become a critical compliance concern for financial services firms and how to build a strategy that keeps your organization aligned with evolving regulations.
How to Protect Your Business From Valentine's Day Phishing Scams
Is your business prepared for the surge in phishing scams around Valentine's Day? Learn how to protect your team and data this season.
Ransomware Recovery Strategies for Financial Services Firms
Effective ransomware recovery for financial services requires comprehensive backup strategies, tested incident response plans, and regulatory-compliant procedures that enable rapid restoration of critical operations.
Understanding Container Security in Modern DevOps Environments
Container security requires comprehensive protection across the entire application lifecycle, from image creation through runtime monitoring and incident response in production environments.
Managing IT Staff Burnout After the Holiday Season
Post-holiday burnout affects IT teams through accumulated stress, delayed projects, and the intensity of returning to normal operations after extended coverage periods.
Essential IT Security Assessment Steps for Financial Institutions
A comprehensive IT security assessment helps financial institutions identify vulnerabilities, maintain regulatory compliance, and protect sensitive customer data from evolving cyber threats.
Leveraging AI-Driven Analytics for Financial Services Risk Management
AI-driven analytics is revolutionizing financial services risk management by enabling institutions to identify emerging threats, predict potential issues, and make more informed risk decisions.